31
UK Web Hosting Offers / All about Remote Desktop.
« on: September 26, 2022, 09:24:46 PM »
All about Remote Desktop.
Have you ever been in a situation where you needed files or programs from a computer that is currently at home or at work? Or the project you are working on was not available while you were in a business trip? All this can be avoided if you have a Remote Desktop. It allows you to connect to your work or personal computer from anywhere in the world and access the files stored on it, or remotely share the screen with friends and colleagues as if you were sitting right in front of it.
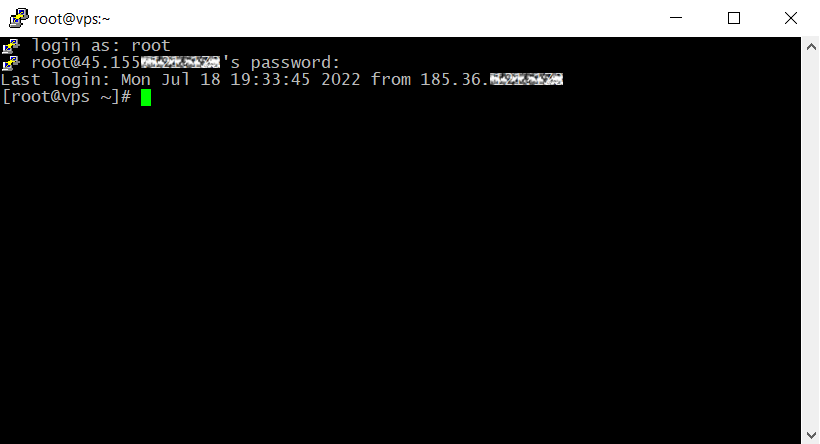
Remote Desktop is a technology that allows you to control a PC or server remotely via the Internet. The connection is implemented by assignment of the administrative rights of your device to be managed by others. The ability to connect from almost any device, be it a PC or laptop, tablet or smartphone, is available due to the fact that the remote server takes the entire workload. You do not overload your device with running processes, but simply get an image from the server screen and freely manage its system.
Remote desktop on a virtual server is necessary for both private use and business. So you have a connection to your home computer at any time and access to your files and soft anywhere. And if you have to work with resource-intensive soft such like video editing, 3D modeling programs or run a video game that your home PC cannot keep up, Remote Desktop can help solve this problem.
For any company, both large corporations and small businesses, it is a great opportunity to organize a remote workplace, allowing you to work from anywhere in the world, having access to corporate software on your work computer and work files. At the same time, all documentation is stored on one server, and access to it does not depend on the presence of the employee in charge in the office. You can perform all actions on a remote device: change software settings, share files, encrypt transferred data, hold conferences, connect webcams, remote projectors and other network devices. It is very important that you have possibility to assign employees access to certain folders.
There are two options for organizing remote access:
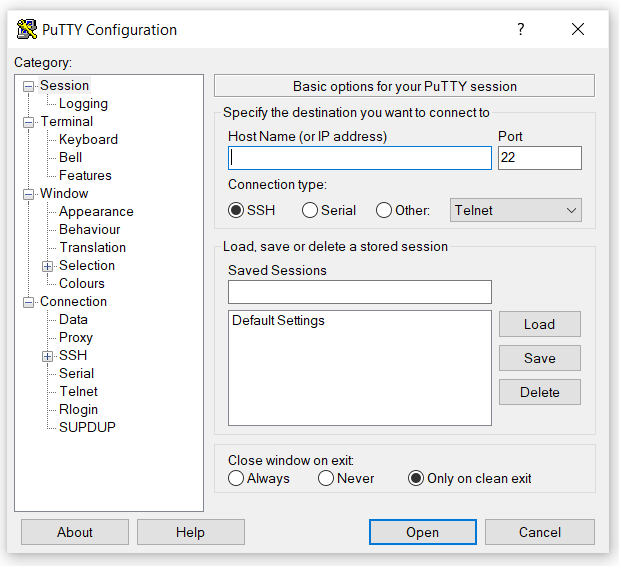
• Special programs that connect two workstations via the Internet. In this case, constant access to power and the Internet are essential.
• Server rental, in which operational activities are performed on a remote server of the hosting service provider (therefore, the requirements for your devices are minimal), and it is accessed via the Internet.
A remote desktop deployed on a virtual server has increased protection, while special programs, both free and with a purchased license, have an increased threat of hacking and unauthorized access to the local network.
Now let's talk more about the areas in which remote desktop on a virtual server has a distinct advantage:
Accounting.
It is well-known that the database should be stored within the company, not at an accountant's home. If you have ever lost your ledgers, or broke the contract with an accountant, then you understand how important is it. With a virtual server, you will always have access to accounting files.
Bank-clients.
For security purposes, some bank clients are linked to the certain IP address and can only be accessed from one device. Virtual servers from LLHOST INC. have dedicated static IP address, which means that your bank account is always available for operations.
Electronic archives.
Remote desktop for the documents' archives contributes to the centralized storage of huge amounts of information. It is great for monitoring, statistics and data management.
Exchange trading.
To keep the network delay to a minimum, the server with bots that buy and sell assets should be located closer to the data centers. For example, LLHOST INC. has a data center in Amsterdam. You connect to the remote desktop from your location, and the bots trade directly from Amsterdam.
Alternative OS.
Some tasks or software may require a different operating system than installed on your device. Virtual servers from LLHOST INC. are the easiest way to deploy it.
System administration.
To system administrators, in order to manage the system and quickly troubleshoot malfunctions, remote access is a must.
Educational platforms.
Distance education is widespread today. Remote desktop technology is actively used by modern educational platforms for remotely students' access.
Personal gaming server.
If you want to set up a server to play online with friends, remote desktop can help in that.
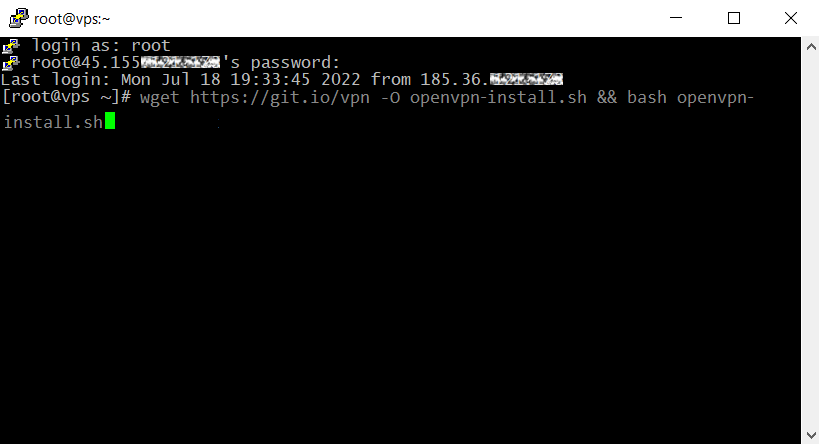
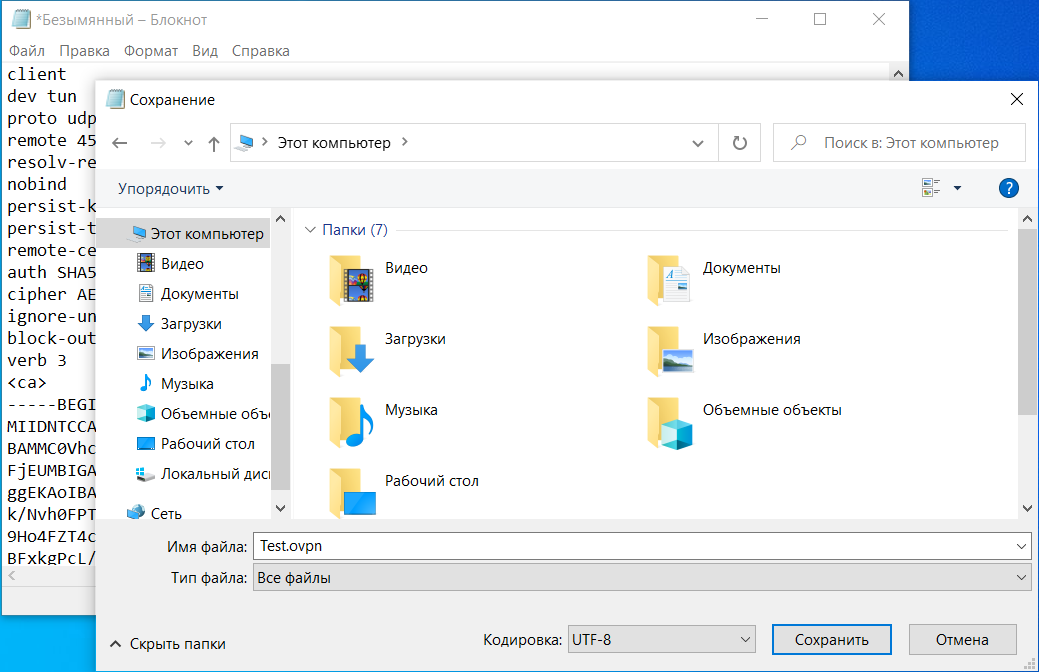
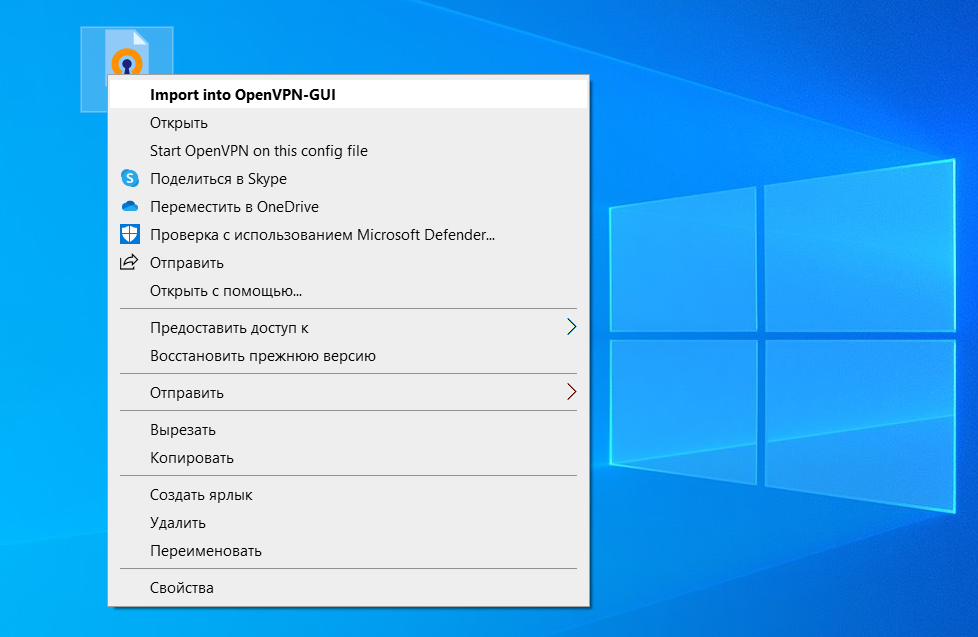
VPN as a Bonus.
You can also deploy your own VPN server based on a virtual server from LLHOST INC. which will be a nice bonus for you.
Remote Desktop is an essential technical tool in almost any area of life. It finds its application for both private and business use, being effective and secure.
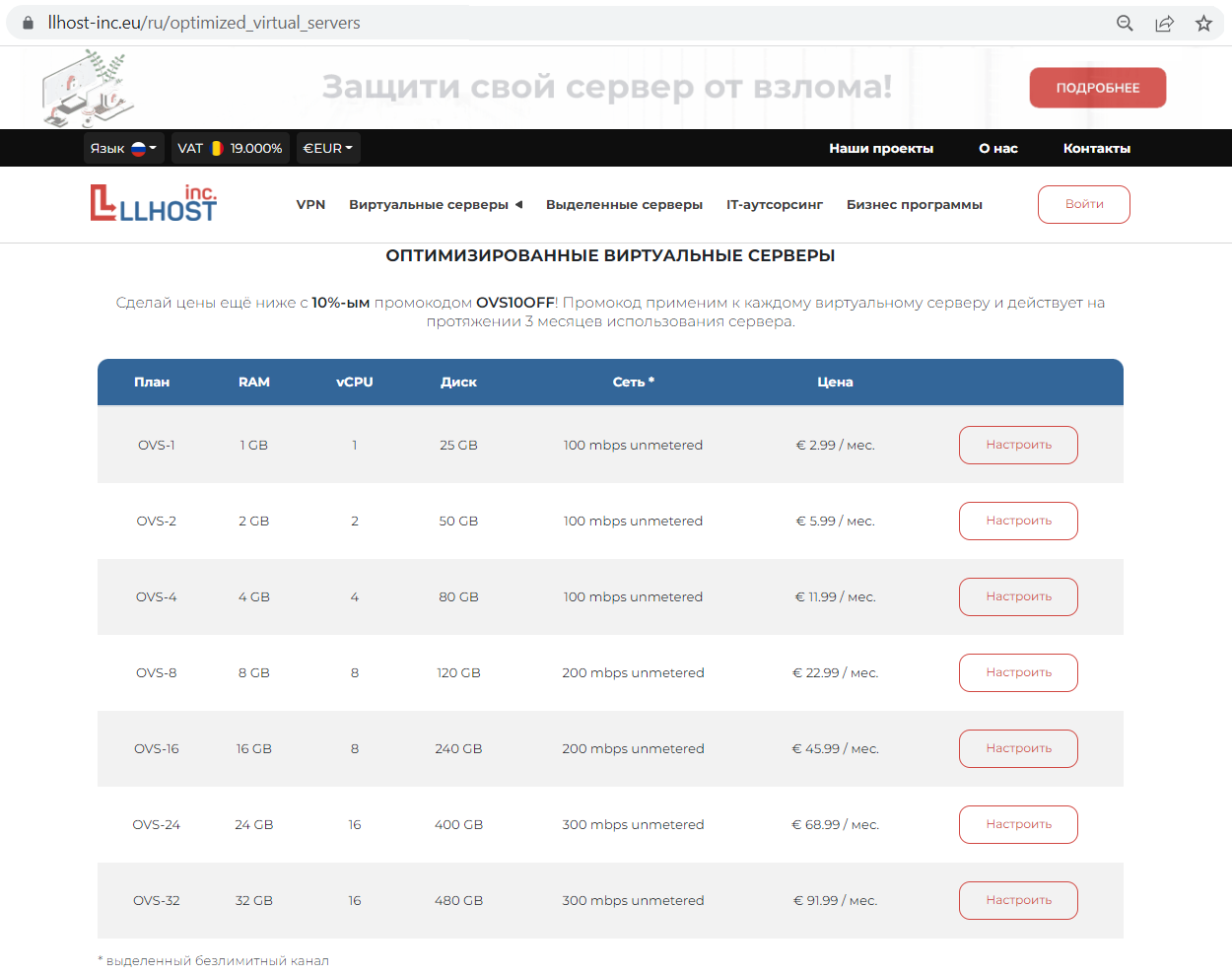
So, today we offer you a -14% discount on any LLHOST INC. virtual server (OVS) plan for three months with the #remote promo code, valid until October 7, 2022. A remote desktop based on OVS from LLHOST INC. is the best prompt solution to boost the PC performance without any substantial investments.